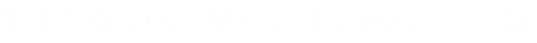
"The fight against crime in cyberspace requires intense coordination and collaboration among all the agencies and institutions involved in it"
Carmen P. Flores
Elvira Tejada de la Fuente is a woman of strong convictions, with a professional career that many colleagues in the profession envy. since 2011, she has been the Prosecutor of the National Coordinating Chamber of the Spanish Prosecutor's Office in the area of computer crime. Previously, she was attached to the State Attorney General's Office as chief prosecutor of the Technical Secretariat. She has participated actively in the implementation and operation of a network of specialist prosecutors. She is a woman in love with her work, to which she dedicates many hours.
What is considered to be a computer crime?
In itself, the concept of Computer Crime is imprecise because the constant evolution of technological tools and their widespread use by the general public leads to the emergence, continually and in the light of these circumstances, of new situations deserving criminal sanctions. Therefore, the concept of computer crime should not be restricted to a specific and predetermined catalogue of crimes, but rather refer to a pluri-offensive and transversal criminal reality with the capacity to affect multiple legal rights of quite different natures. Among them, some are of a personal nature, such as honour, privacy or sexual freedom and indemnity of minors -affected in the crimes of child pornography or child grooming-, others with an economic content -in the case of computer frauds or attacks on networks or information systems- and even at times, collective or supra-individual interests, as in the cases in which technological tools are used, and the Internet in particular, for terrorist purposes or as a means of disseminating hate messages, violence or intimidation about those who are different. Therefore we are facing illicit phenomena that are quite different from each other, but in which there is as a common denominator, a determining circumstance. This is precisely the relationship between criminal activity and the information and communication technologies themselves (hereinafter IT), either because they constitute the object of the crime or because they are the means through which criminal activity is carried out.
Consequently, there is no uniform, internationally accepted criterion of what should be understood by Computer Crime, although we should note that that the Convention on Cybercrime of the Council of Europe, published in Budapest in 2001 with the purpose of establishing the bases of a common criminal policy when facing Cybercrime. In its Chapter II, it includes a first definition of what is to be understood by such a category. This is specific in the following criminal behaviours:
- Crimes against the confidentiality, integrity and availability of data and computer systems, a section that includes the different criminal types that punish attacks on information systems.
- Computer Crimes, a section that includes computer falsification crimes and those of computer fraud.
- Crimes related to content, a section that includes crimes related to child pornography.
- Offenses related to intellectual property infractions and other related rights.
A good example of the constant evolution that we mentioned earlier is the fact that this initial catalogue was immediately extended with the publication of the Additional Protocol to the Convention itself in 2003, which penalizes acts of a racist and xenophobic nature committed by means of computer systems. For the same reason, the efforts carried out within the Convention are permanent, updating and adapting their text to the variation of the situations that occur as a result of technological development.
This inaccuracy in the delimitation of the concept of Computer Crime explains the State Attorney General's approach when defining the area of specialization established on this matter in the Public Prosecutor's Office. Thus, Instruction 2/2011 on the Criminal Prosecution Investigative Department and the computer crime sections of the Prosecutor's Offices establishes the scope of competence in this area of specialization based on the following parameters:
- Crimes in which the object of the criminal activity is the data itself, computer systems or IT in general, as is the case of illegal access to systems, computer damage or crimes against broadcasting and interactive services.
- Crimes that protect different legal assets, whose characteristic is that IT is used to carry out the criminal activity. Such is the case of the crimes of computer fraud, child grooming, child pornography or attacks against intellectual property committed through the services of the information society.
- Any other kind of crimes committed through IT when these tools are an essential element in the planning and carrying out of criminal action and determine a level of complexity in investigation that requires the intervention of specialists in that field. This section could include a variety of criminal offenses such as crimes against the honour and privacy of individuals, against freedom, heritage, falsehoods, hate crimes and in general any criminal behaviour that meets the indicated characteristics.
As can be seen, based on these parameters, the Office of the Attorney General of the State has opted for an "open" concept of cybercrime that allows adapting the skills of the area of specialization to the evolution of this form of crime.
Is Spanish legislation up to date to act against cybercriminals?
In Spain, it is actively working, together with the other EU countries, to make possible the safe use of cyberspace in which the rights and liberties of the general public and the legitimate interests of Countries are duly safeguarded. A good example of this is the approval in December 2013 of our National Cybersecurity Strategy that follows the parameters defined in the European Strategy on the same subject and in which both preventive and repression aspects and sanctions of the behaviours are addressed. make them subject to criminal reproach.
Undoubtedly, other examples of the effort to adapt national legislation to these objectives are as yet still work in progress to accommodate our Organic Law on Data Protection to the new European Regulation 2016/679 of April 27th on similar related matters to the implementation in Spain of the Directive (EU) 2016/1148 of July 6th, whose purpose is to strengthen the protection of networks and information systems.
With regard to the aspects related to the investigation, prosecution and criminal sanction of illicit activities associated with the irregular use of IT, the legislative changes that took place in 2015 are particularly significant. This reform of the Penal Code by the Organic Laws 1/2015 and 2/2015 of March 30 gave new regulation according to current necessities to many of the crimes within the scope of cybercrime: child pornography crimes; illegal access to systems and computer damage crimes; crimes against personal privacy; intellectual property crimes, and terrorism and hate crimes, among others.
Also in the same year 2015, n significant revision of our old law of Criminal Procedure was carried out, whose consequences were precisely the complete and detailed regulation -by LO 13/2015 of October 5th- of the use of technological tools for the pursute of crimes and the determination of their perpetrators. These new tools are extremely useful against cybercrimes and the legislator has managed to articulate their operation as a means of criminal investigation, whilst at the same time respecting the demands and guarantees of the Rule of Law.
In both cases, the changes that have taken place in the internal legal order follow the guidelines and guidelines of the European regulations on the subject, specifically the aforementioned Budapest Convention and the different directives issued in recent years in the European Union.
Are more legislative reforms necessary?
As indicated when answering the first question, it is evident that the constant evolution of technologies continuously generates new situations to which, in many cases, we will need to provide legal responses. Consequently, the need for new legislative initiatives will be continuous and permanent, both in our own country and in others.
From our point of view, the response of the Rule of Law to these situations that are generated as a result of technological advances requires an agile legislative development that adapts legal norms to an unquestionably changing reality. To this end, it is essential that this process be sustained internally, with the active participation of those who operate in the multiple sectors involved in it, both from public administrations, as well as from the private sector and with participation also from the general public because, as we have indicated, we are facing a reality of transversal nature that affects many aspects of social and economic activity.
In turn, and from a transnational perspective, an adequate level of coordination with other countries is also necessary, since in its planning and execution, cybercrime goes beyond national territorial limits. We have to seek the convergence of different countries' legislations, in accordance with internationally accepted guidelines and criteria, to articulate this necessary "common language" that fosters and facilitates close cooperation between the authorities responsible for this matter in the different territories to offer common, or at least coordinated solutions, responding to a criminal phenomenon of indisputable transnational character. In this work, international organisations and institutions with responsibility in the matter can also have an significant role.
In any case, it is unquestionable that legislative initiatives of an internal nature or those adopted in transnational geographical frameworks, as well as strategic or operational actions in response to cybercrime, should be centred on respect for fundamental rights and freedoms of the general public, as well as the principles and values that our legal and social order is based on, in such a way that they are fully adapted to the parameters of the Rule of Law.
What is the role of the network of Prosecutors specialized in Computer Crime?
In the first place and in general, we have to remember that the Public Prosecutor's Office, as stated in art. 124 CE, among its functions is to promote the action of justice in defence of the legality of the rights of the general public and the general interest. This function is specified in the criminal process in the exercise of criminal action against crimes that can be prosecuted ex officio and also in the defence and protection of the victims of these behaviours.
In 2011, the Spanish Public Prosecutor -following a common approach to other areas of activity- put this area of expertise into operation with the aim of offering a more specific and effective response to computer crime from the Prosecutor's Office under the terms indicated above. This area of expertise is integrated into a central unit based in Madrid and the territorial services established in each of the Spanish provinces and is currently composed of about 150 prosecutors who assume the task of promoting investigation and directly intervene and coordinate the action of the Prosecutor's Office in the processes for this type of crime.
One of the main missions of this Institution is to promote and favour the uniformity of criteria in the interpretation and application of standards as a means of guaranteeing legal security and equality of all the general public in the eyes of the law and this is referred to in article 124 of the EC to consecrate the unit of action as one of the informative principles of the Public Prosecutor's Office. To that end, the Prosecutor's Office works as an extended team in which the position taken in response to the legal issues that arise in the development of the entrusted activity is carried out based on joint work and reflection. Therefore, one of the most significant missions of those who integrate this area of expertise is to delineate -based on the experience and knowledge acquired in the daily work against cybercrime- those common criteria that serve to reinforce this aforementioned principle of unity of action. These criteria for action, once taken on board by the Attorney General's Office, are public knowledge for all the general public and have to be taken into account by all Prosecutors in the exercise of their functions.
But also this team action, to which I referred earlier, also serves other objectives. On one hand, for the coordination of investigation, because frequently, the illicit acts carried out through the Internet cause harm to many people in different places of Spain and, even beyond our borders, giving rise to a diversity of investigation and judicial proceedings referred respectively to the different consequences of the criminal act in question. The work we do is to coordinate this investigation, seeking whenever possible to compile and consolidate them into a single procedure that guarantees an adequate response from the Rule of Law to such illicit acts, proportional to their seriousness and consequences.
This specialized action, and the direct intervention in this investigation, also provides us with knowledge -underpinned by real data- of the incidence of this criminal phenomenon, as well as of its evolution in its different manifestations, both nationally and in each of the territories of the State. This information, along with our suggestions on future legislative reforms in relation to it, are compiled annually in the State Attorney General's Office Report. This is transmitted to the National Government as well as to the legislative bodies, so that they can assess the definition of criminal policies on this matter.
Finally, it is evident that specialization and teamwork favour and strengthen collaboration with other agencies and institutions with responsibility in this field, and in particular with the Security Forces and Bodies whose extraordinary work constitutes one of the essential supports in carrying out our function. However, it also facilitates being closer to those who are victims of these behaviours and particularly to the general public who can find qualified and expert people in the Prosecutor's Office whose function is precisely to protect their interests and the interest of society in general.
In short, the specific training of the members of this group of Prosecutors and their preferential and specialized attention in this area, with impartiality and full submission to the Law, have made this area of expertise the "spearhead" in carrying out the function that corresponds to the Public Prosecutor's Office in response to this form of delinquency and specifically in promoting and revitalizing criminal investigation and exercising -when there are indications of an illicit act being committed- the penal actions against those responsible for the crime, at the time and in particular, attending to the protection and defence of the rights and interests of those who have been harmed by the criminal action.
How many cases have there been of computer crimes in 2016?
According to the latest State Attorney General's Office Report, the number of proceedings initiated by the judicial bodies in 2016 for unlawful acts within the scope of computer crime -as previously defined- amounted to 8,035 nationally. As a first premise, we should clarify that this figure has to necessarily differ from the Security Forces' and Corps statistics since, after the reform of article 284 LECrim (Law on Criminal Procedure) at the end of 2015, the police units have to transfer to the judicial organs or to the Prosecutor's Office only those cases with known perpetrators, or at least those likely to be identified. This circumstance has determined that the volume of judicial records for acts of this nature has been reduced considerably with respect to the previous years.
Of the total of these procedures, 61.35% -4,930 of them- were for behaviours generally enshrined in the crime of fraud in its different manifestations, criminal typologies that generate, year after year, the most significant volume of investigations, in the that we group together a diversity of fraudulent manifestations, from the most traditional based on the deceit of the victim -no doubt facilitated by the diffusion capacity inherent in the use of IT- to the novel and ever-changing possibilities offered by the technological tools to achieve a non-consensual displacement of patrimony to the detriment of another, through computer manipulations or artifices of a similar nature.
Undoubtedly, the number of legal proceedings initiated for crimes against the freedom and security of people, crimes of threats, coercion or harassment, committed through these technologies, which in 2016 totalled 1,120 invocations, almost 14% of their total, and the figure corresponding to the investigation into unlawful acts that attempt, through IT, against the freedom and sexual indemnity of the minors is also relevant, which in 2016 gave accounted for 779 criminal investigation files, 9.70% of the total of those initiated by illicit activities linked to the use of IT. In both cases, these are particularly serious behaviours since they affect personal legal rights and put at risk the free exercise of the rights and freedoms of the general public.
Also deserving of special mention are the processes of criminal activities linked to attacks on the information systems, which generated 682 new cases last year -an 8.48% of the total-. This figure is quite small compared to the overall volume of the data on security incidents officially published. Notwithstanding the record that not all of these incidents meet the necessary requirements to be considered a crime, the data obtained shows that a good part of these criminal activities are hidden, mainly because of the lack of complaint of those who are harmed by these attacks. Other data of interest for this purpose are the 54 procedures initiated to investigate crimes against intellectual property committed through IT, and the 99 that were aimed at behaviours in which these tools were used for the dissemination of a hate discourse.
What importance do you give to the unification of the assessment techniques of the different bodies so that there are no dysfunctions?
Without doubt, the fight against crime in cyberspace requires a concentrated coordination and collaboration between all the agencies and institutions involved. As we have already indicated if intense work is being done between the different countries to achieve a common strategy and regulation, with the aim of facilitating joint work in response to these illicit activities whose trans-frontier character is evident, how much more should be sought in the internal effort, as regards an effective collaboration between the different organisms and institutions involved in this matter?
The rapid evolution in the criminal manifestations of the irregular use of technologies; its impact on a variety of legal assets; the complexity involved in its investigation and the territorial dispersion inherent in the actions that occur in cyberspace, makes this union of efforts absolutely essential to be in a position to provide effective responses to this new form of crime.
The Prosecutor's Office has fully accepted this approach, and therefore, since the constitution of the network of Special Prosecutors, mechanisms of work and permanent communication with the different police bodies have been put into place. In fact, since 2014 at the headquarters of the Prosecutor's Office we have different liaison offices with the units expert in technological investigation of the National Police and Civil Guard, while maintaining regular and close contacts with the specialists of the police bodies of the Autonomous Regions. The collaboration thus articulated not only towards the analysis and valuation of specific investigation but also to the joint search for solutions -from the exchange of technical and legal knowledge- to the questions that are arising in implementing the new criminal types or in the use of technological tools for criminal investigation with the objective, in any case, of improving our effectiveness against cybercrime, while respecting the principles and guarantees inherent to the rule of law.d guarantees inherent to the rule of law.